Cyber Security Diagram
Cyber security management system asset software solution gas oil diagram guardian operators leading network solutions Cyber framework template Network security diagram
cyber-security-diagram-1148
Diagram security cyber 1148 Cyber security Cyber security degrees
Network security diagrams
Diagram cybersecurity previewDiagram of cybersecurity stock illustration. illustration of access Security network diagram architecture example firewall cyber diagrams clipart model microsoft conceptdraw recommended examples computer degrees infrastructure structure secure devicesSecurity cyber framework diagram ignite detect respond protect recover systems categories csf five.
Security network diagram diagrams computer efs operation networks solution example conceptdraw architecture encryption system networking secure between cybersecurity application microsoftCyber security Laptop security infographic diagram (cyber security)Cyber security st. louis.

Controls cybersecurity
Laptop slidemembersSecurity cyber dimensions ten chemical facility diagram performance Cyber security management system software solution for one of the worldCyber security hacking ethical phases vs four mainly given below different there.
Cybersecurity diagram previewCyber security Security cyber powerpoint diagram shapes templates slides step slidemodel boardCyber security framework.
Cyber security vs. ethical hacking
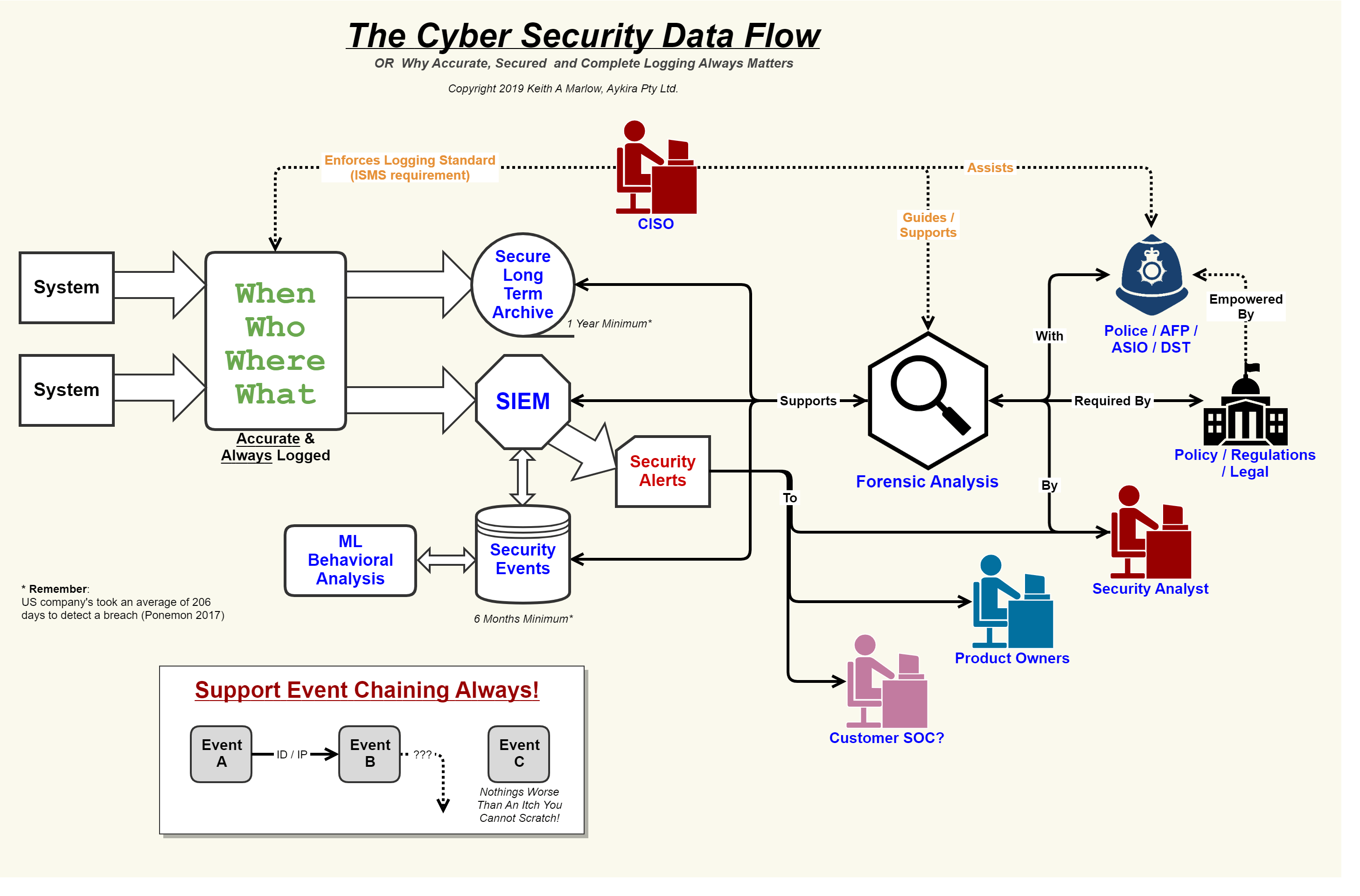
Cyber lynxDiagram of cybersecurity stock image. image of presentation Diagram-cyber-security- — io solutionsSecurity flow cyber data event logging diagram logs internet important why so together showing concerning events au.
Cyber octNetwork security devices Diagram of cybersecurity stock image. image of controlCyber security.

Cyber security framework mind map template
Cyber security secure network diagram building controls systemsSecurity cyber cybersecurity technologies information threats examples steps Cyber security network tips computer infographic diagram diagrams steps degrees cybersecurity example conceptdraw networks solutions architecture risks threats information clipartSecurity event logging, why it is so important – aykira internet solutions.
Security network diagram model cloud diagrams government computer devices solution conceptdraw access example networks architecture cybersecurity information models solutions examplesMonitored managed continuously Cyber security visualize threats and vulnerabilitiesChemical facility security news: an interesting systems look at.

Cyber security degrees
Security network diagram control devices access diagrams computer encryption networks solution secure model flowchart conceptdraw example area examples cloud system4 step diagram for cyber security .
.







